The AI-Driven Hardware Security Module (HSM) is revolutionizing digital protection in 2025. As cyber threats become smarter and more adaptive, organizations need security systems that can think, learn, and react. Combining artificial intelligence (AI) with hardware-based encryption allows systems to detect anomalies, predict attacks, and respond automatically — all in real time.
If you manage sensitive data, digital transactions, or enterprise systems, adopting AI-Driven HSMs is now essential for robust cybersecurity.
Table of Contents
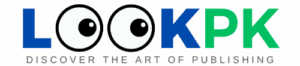
🔍 What Is a Hardware Security Module (HSM)?
A Hardware Security Module (HSM) is a physical device that safeguards cryptographic keys and performs encryption or signing within a secure, tamper-resistant boundary.
- Secure key generation, storage, and lifecycle management
- Hardware-accelerated encryption and signing
- Compliance with FIPS and PCI-HSM standards
- Used in banking, authentication servers, and cloud platforms
For a deeper understanding, explore IBM’s official HSM documentation.
🤖 Why AI Is the Future of Hardware Security
Traditional HSMs are static — they execute rules but can’t adapt to new threats. By embedding AI, the AI-Driven Hardware Security Module becomes dynamic, learning from usage patterns to identify unusual behavior and block attacks before they happen.
Key Benefits of AI-Driven HSMs:
- Real-Time Threat Detection — AI monitors cryptographic behavior for anomalies.
- Predictive Risk Analysis — Detects potential threats early using data models.
- Adaptive Key Management — Automatically rotates or revokes keys based on AI logic.
- Reduced Human Error — Eliminates misconfigurations via automated learning.
- Continuous Learning — The more data it processes, the smarter it becomes.
Learn more from ResearchGate’s study on AI intrusion detection.
🧠 How AI-Driven Hardware Security Modules Work
An AI-Driven HSM combines physical cryptography with intelligent software. Inside the device, an AI analytics engine observes operations, flags suspicious patterns, and enforces security policies autonomously.
- AI algorithms for behavioral analysis
- Secure telemetry capturing internal signals
- Verified AI model updates with cryptographic signatures
- Fail-safe fallback to classic HSM operation
This creates a self-defending cryptographic environment capable of independent decision-making.
🌍 Real-World Applications
- Cloud Providers: Detect cross-tenant misuse in data centers.
- IoT Security: Protects millions of smart devices at the edge.
- Banking & Finance: Prevents fraud and unauthorized digital signatures.
- Firmware Validation: Secures software supply chains from tampering.
- Ransomware Defense: Blocks unauthorized encryption attempts instantly.
Explore related insights from NVIDIA’s AI research lab.
⚠️ Challenges
- AI Model Attacks — Poisoning or evasion attempts must be mitigated.
- Performance Impact — AI inference adds computational overhead.
- Certification Gaps — Regulatory standards are still evolving.
- Auditability — Explainable AI is crucial for compliance validation.
For certification guidance, see NIST’s FIPS 140-3 standards.
🔮 The Future of AI Security
AI-Driven Hardware Security Modules will soon power autonomous cryptography, federated learning, and quantum-resistant protection. Expect tighter integration with zero-trust architectures and blockchain verification for global security ecosystems.
Discover related innovations on LookPK AI Tools or explore LookPK Security Tools.
🏁 Conclusion
The AI-Driven Hardware Security Module (HSM) blends human intelligence with machine precision — a future-ready defense mechanism for a digital world. As threats evolve, these intelligent modules ensure encryption remains unbreakable and adaptive.
Stay ahead with advanced AI cybersecurity insights on www.lookpk.com